F5 report: 390 abandoned .ics domains put nearly 4M Apple devices at calendar‑phishing risk
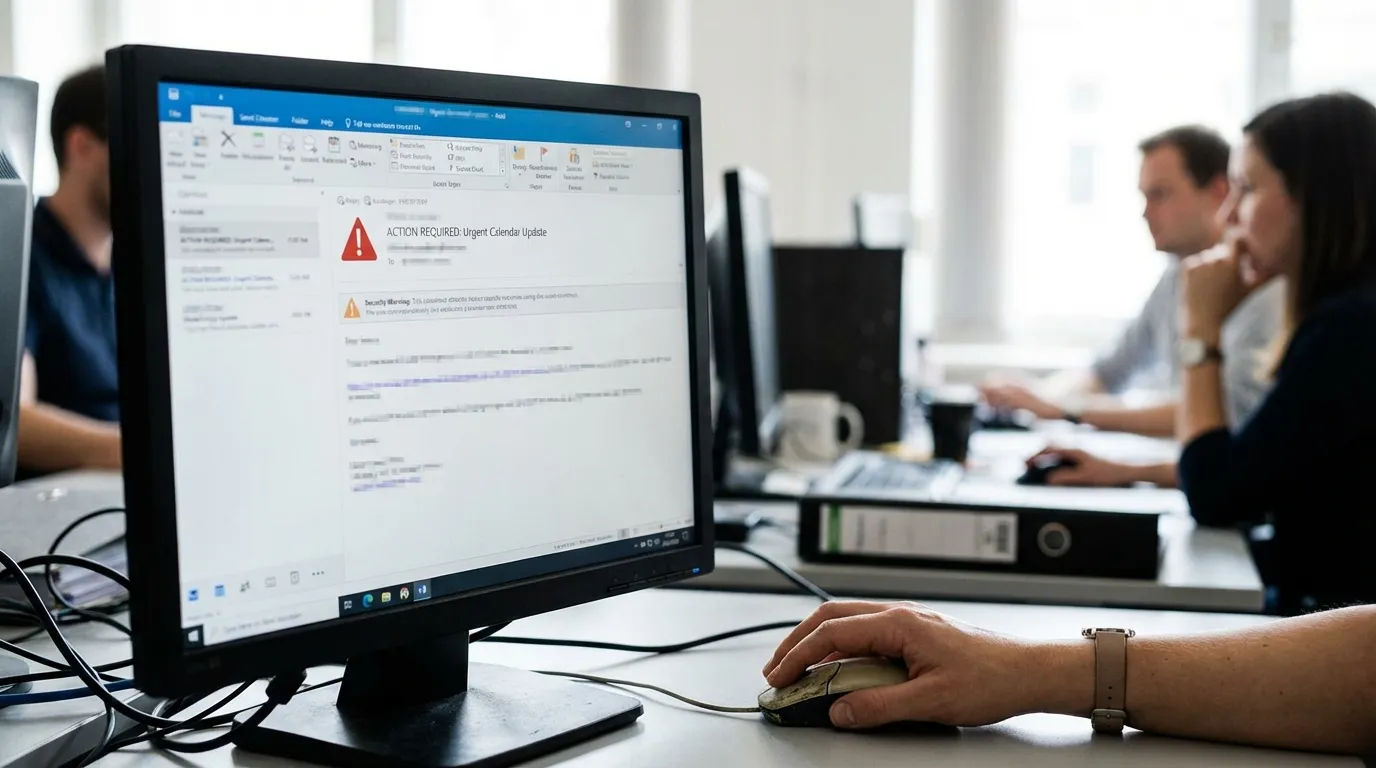
Researchers reported that over 390 expired or hijacked .ics/calendar sync domains are still active and are queried by nearly 4 million iOS and macOS devices, creating an attack surface for calendar‑based phishing and spam. Security teams advised reviewing calendar subscriptions and implementing filtering and monitoring because malicious calendar updates can bypass some email and web protections.
An F5 Threat Report found more than 390 abandoned, expired, or hijacked .ics/calendar sync domains that remain reachable and receive queries from almost four million Apple devices. Attackers who register these dormant domains can push malicious calendar updates containing phishing URLs, spam events, or prompts engineered to trick users into installing malware or enabling persistent notifications. Because calendar subscriptions are often trusted and bypass standard email gateways and web proxies, malicious events can reach users without triggering conventional threat detection. F5 analysts warned that organizations and individual users should audit and remove unfamiliar calendar subscriptions, enforce stricter filtering of .ics feeds, and normalize Unicode and URL encodings in calendar parsers to prevent obfuscated lures. They also recommended monitoring DNS and domain registration trends for expired calendar endpoints, applying endpoint protection to catch secondary payloads, and educating users to treat unexpected calendar event invitations with the same suspicion as unsolicited emails. Network defenders were urged to integrate calendar subscription checks into security monitoring and incident response playbooks to close this emerging vector.
Related Scam Types
Related Articles

Researchers flag 4,300+ FIFA 2026 domains used for ticket, streaming and crypto scams ahead of World Cup

FBI launches Operation Winter SHIELD to harden private‑sector defenses against cybercrime and fraud

